Keeping the world safe from cybercrime is big business, and the growing number of players are looking for more ways to compete and win. The rewards could be substantial. According to Fortune Business Insights, the cybersecurity market is expected to swell to more than $282 billion annually by 2027, an annual growth rate of over 12 percent.
The reasons for this massive growth include the increasing prominence of e-commerce, artificial intelligence, the “internet of things,” and blockchain technology. The threat landscape also continues to expand, with increasingly sophisticated attacks targeting everything from critical infrastructure to everyday operations. To keep up—and keep safe—companies and governments have no choice but to devote a growing share of their IT budgets to cybersecurity.
The cybersecurity market is dominated by many of the long-time leaders in technology, such as IBM, Microsoft and Cisco, as well as niche cybersecurity providers like Symantec and McAfee. But exponential growth inevitably attracts new entrants; Fortune Business Insights estimates that the small and midsize players will see the fastest revenue growth in the years ahead.
We’ve had a front-row seat at this cybersecurity derby. In the past few years alone, we’ve rebranded several innovative cybersecurity companies in very different segments of the industry. All of them came to us with the same request: help us to stand out and above the competitive noise by defining and communicating a sustainable and authentic point of differentiation.
Each of these companies faced unique circumstances in their quest to make an impact. But our experience working with them uncovered five fundamental imperatives that any cybersecurity leader must understand to build a successful brand.
The Five Key Imperatives for Cybersecurity Branding Success
Cybersecurity Branding Imperative #1: Forget FUD
For decades, fear, uncertainty, and doubt (FUD) dominated cybersecurity messaging. “Be afraid, be very afraid” was the prevailing narrative, often backed by dark imagery and alarming statistics.
While it succeeded in raising awareness about cyber threats, today’s reality has rendered this approach less impactful. Cyber threats are no longer abstract dangers—they’re a daily, well-documented risk. High-profile breaches and systemic vulnerabilities regularly dominate headlines, making FUD-based branding more redundant than reassuring.
Understandably, some brands may argue that fear remains an effective motivator. In working with our cybersecurity clients, we found that FUD branding was so deeply entrenched that companies often resisted relinquishing it until research proved conclusively that it no longer resonated with their prospects. But while fear may grab initial attention, it rarely builds the trust and confidence that are essential for lasting relationships with B2B audiences.
CISOs, CIOs and boards no longer want reminders of what’s at stake; they already know. What they want are solutions—and partners—that empower them to act decisively and protect proactively.
Cybersecurity Branding Imperative #2: Aim High
You would think that achieving safety and security would be the most important motivator of all, whether in one’s personal life or in business. But in fact, there is abundant research showing that security—while important—doesn’t rank high among human needs.
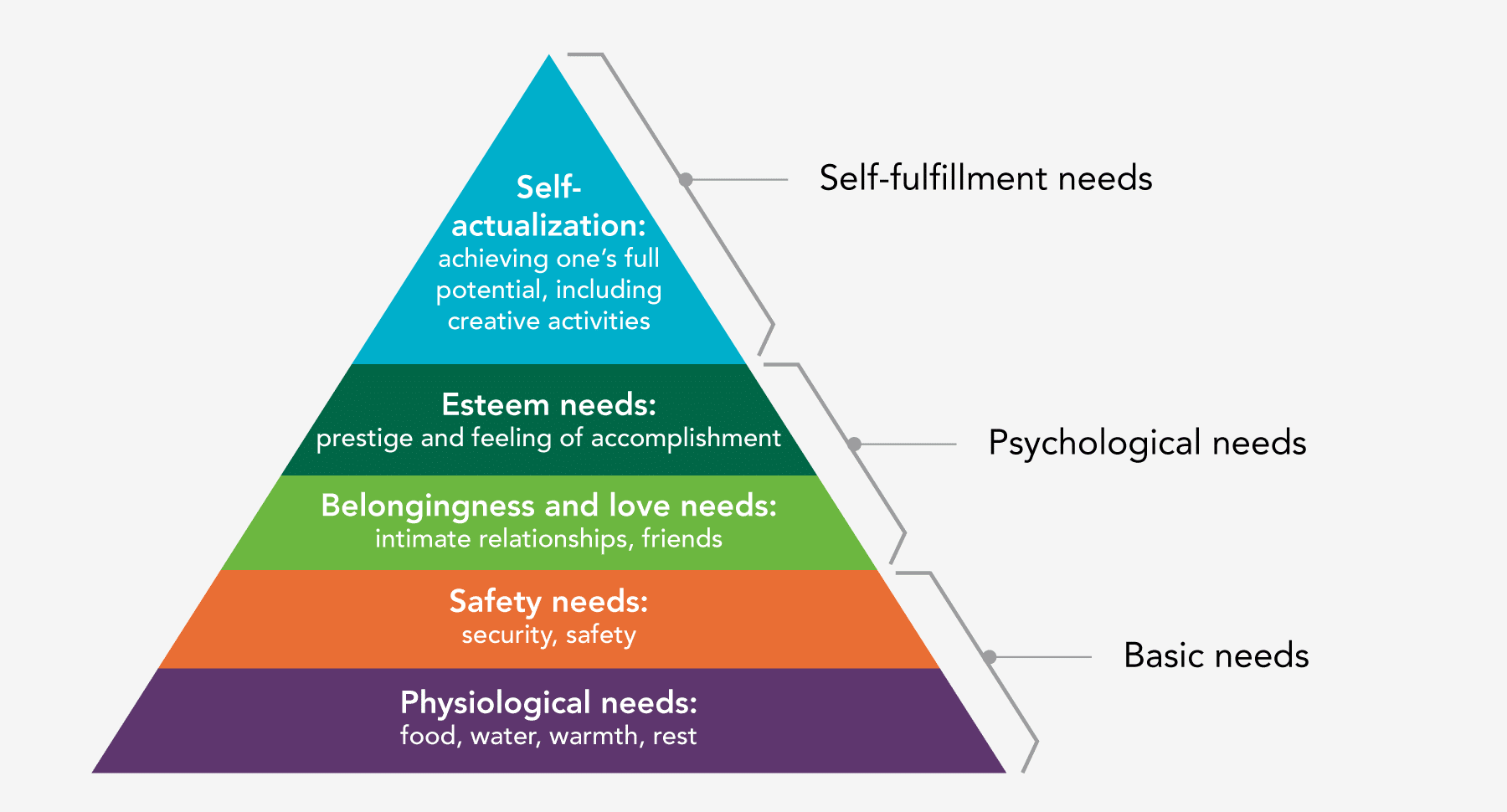
Perhaps the best-known proponent of this idea is Abraham Maslow, the American psychologist whose “hierarchy of needs” remains a widely accepted theory of psychological health. Maslow’s hierarchy is composed of a five-tier model of human needs, often depicted as levels within a pyramid. Needs lower down in the hierarchy must be satisfied before individuals can attend to needs higher up.
At the base of the pyramid are physiological needs like food and water; just above these are security and safety. Higher up we find the need for prestige and a feeling of accomplishment. At the very top of the pyramid is self-actualization—achieving one’s full potential.
Viewed in the context of cybersecurity, safety and security are necessary to achieve a sense of satisfaction but are not sufficient to drive all decision making. This is why a cybersecurity brand that appeals only to a desire for safety won’t resonate at a deep level with the marketplace; even in a B2B context, decision makers are looking for a sense of achievement for both themselves and their organization.
A successful cybersecurity brand strategy appeals to a higher-order need that can deliver this feeling of accomplishment. In the B2B context, this might be the confidence to expand a business to new geographies or into new market categories. The brand could also appeal to the self-actualization needs of the decision makers themselves.
In one partnership, we created and activated a brand for a leading identity management company that addressed the IT buyer’s desire to say “Yes, we can do that” rather than “No, that’s too risky.” to internal audiences—people who come to them with ambitious plans for expansion. The brand appealed to the buyer’s need to act as (and be seen as) a business enabler, not a danger to the organization. It validated their desire for self-actualization.
Cybersecurity Branding Imperative #3: Be Human
Technical specs get you in the room, but human trust and confidence seal the deal. A strong cybersecurity brand simplifies complex offerings and creates a clear, compelling reason for decision-makers to choose you over competitors.
From a branding perspective, we find cybersecurity to be one of the most dehumanized spaces in the B2B arena: lots of diagrams and flowcharts, not many images of actual people. This might not be a problem—after all, many IT professionals have an affinity for data and data visualizations—except for the fact that cybersecurity buyers also seek reassurance that the solution being offered actually works (and will continue to work) as threats multiply.
But as much as IT decision makers are looking for today’s data, they’re looking for a reason to believe. Consider these common, urgent questions—and how a strategic cybersecurity brand can answer them in ways that feel more human:
- Q: How will the solution stay one step ahead of the bad actors?
A: The people behind the solution are continually monitoring the landscape to anticipate what’s coming - Q: Who will answer my questions and address my concerns?
A: The same people who stand behind the solution - Q: Why is this solution superior to the other solutions that claim to do the same thing?
A: Because the people who created it are smarter, more responsive, more experienced
Putting people front and center not only provides critical reassurance to prospects, it can also help to differentiate. But to be effective, the brand can’t simply be about photos of smart-looking people looking pensive in front of computer screens. It needs to be about expertise and experience. So brands also need to offer by-lined white papers, video interviews, speaking engagements, and website bios that go deeper than listing accomplishments and degrees.
In combination, all of these give prospects reasons to believe that the solution will perform as promised—today and tomorrow.
Cybersecurity Branding Imperative #4: Play Well with Others
In the B2B world, one solution—even one company—can never provide all the cybersecurity necessary to protect the enterprise.
Our research has shown repeatedly that “one-stop shop” is almost never a strong benefit for IT buyers; they prefer to acquire best-of-breed solutions from however many vendors it takes. Whether it’s end-point solutions, network security, cloud application security, identity management or antivirus protection, the chief information security officer (CISO) and other IT buyers are more than happy to pick the solution they think works best from the provider they trust, provided it works with their existing (often myriad) solutions.
In this cluttered environment, a cybersecurity brand that effectively communicates how it integrates seamlessly into existing ecosystems underscores its technical reliability as well as its innovation—proving that your team understands this real-world challenge for buyers.
Of course, every successful cybersecurity company provider builds interoperability into their solutions. And they always make a point—and often a big point—of touting this. But cybersecurity brands need to do more than say they play well with others. They need to show it in a way that goes beyond complex IT infrastructure diagrams.
In words and images, the brand needs to convey openness, approachability and collaboration. The company’s core values need to reflect this spirit of cooperation, and core integration promises need to be infused into the brand.
At the same time, the cybersecurity brand should, ideally, communicate that it not only works with other solutions, it can actually make them more effective. IT executives are all too often forced to plead with skeptical CFOs and boards of directors for additional funds for yet another cybersecurity solution. Their case would be easier to make if they could demonstrate that the latest solution they’re advocating can actually enhance the ROI on existing ones!
A few years ago, we developed a brand for a managed solutions provider that communicated just this message. The brand positioned itself successfully as the catalyst that—when added to the already complex (and expensive) cybersecurity ecosystem—unlocks the true potential of all the component parts.
Cybersecurity Branding Imperative #5: Make It Personal
Finally, a cybersecurity offering must appeal to a diverse range of audiences:
- The CISO will want complete assurance that the solution works effectively, offering the right features and functionality
- The CIO will be less interested in details of the solution and more concerned with its impact on other components of the enterprise’s IT infrastructure
- The CFO will want to know the anticipated ROI, including the cost of not making the investment
- The Board of Directors will insist on assurances that this product will protect the enterprise’s value and, just as importantly, its reputation
Alas, every company in our connected world gets just one brand, so the brand must resonate with buyers and influencers who have different (and in some cases conflicting) agendas. The challenge is to develop a brand that appeals to all audiences without falling victim to the “lowest-common-denominator” trap: a brand that’s so general and watered down that it essentially says nothing to anyone.
We’ve seen this happening across the cybersecurity landscape; brands either go “too high” (and general) and become meaningless or “too low” (and specific) and become irrelevant to many, if not most, critical audiences. The solution: create a powerful, resonant brand with broad appeal, and support it with targeted messaging that communicates the brand through the filter of specific audience needs.
For example, our message mapping methodology identifies a core group of messages, usually no more than five or six, which are universally applicable. We then “map” a series of messages that target each key audience with a tailored value proposition that supports, and is supported by, the overarching brand.
In this way, the brand achieves consistency and relevance across audiences and at every communications touchpoint.
Building a Cybersecurity Brand That Leads
Cybersecurity providers are in the enviable position of selling to a huge and growing market, and one that is increasingly seen as essential to the health of companies, governments and the economy overall.
Yet as the market becomes even more saturated with competitors and threats only become more complex, it faces an inflection point. Growing market share now requires more than technical expertise alone, and leaders must embrace brand as a platform for value creation.
Brands that rise above the fray will have a unique opportunity to lead in technology as well as trust, connection and innovation. By focusing on what truly matters—moving beyond fear-based messaging, appealing to higher-order needs, humanizing your brand, demonstrating collaboration, and crafting tailored messaging—they can unlock new possibilities for growth and market leadership.
Each organization will need to identify the brand opportunity that’s authentic to its offering and core values, and can set them apart. Brand research, along with an in-depth competitive analysis, is always indispensable in this process.
That said, while every cybersecurity brand will be—and should be—unique, we’ve found that starting from a foundation of these five imperatives will help to ensure the strongest outcome: a compelling brand that resonates with the people who matter most.
Want to discuss the five imperatives and B2B cybersecurity branding in more depth? Let’s talk.
Subscribe to Our Newsletter
Originally published April 10, 2020.